PDF) A study of DC electrical breakdown in liquid helium through analysis of the empirical breakdown field distributions
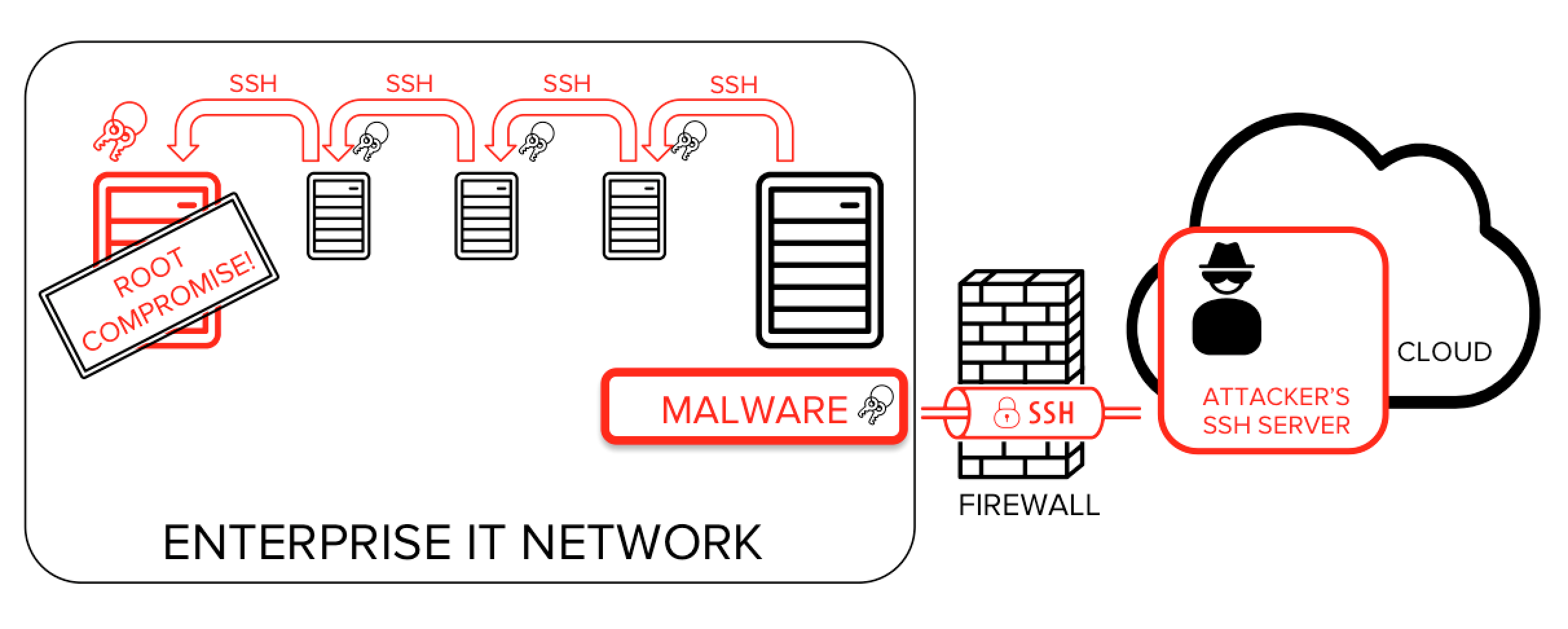
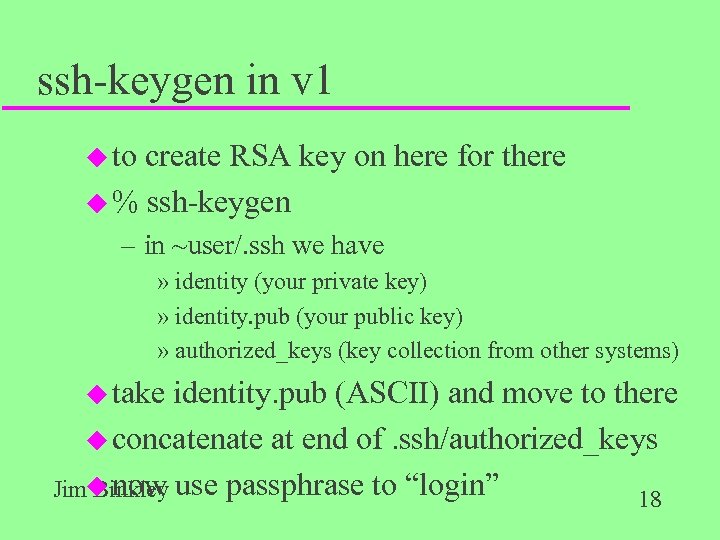
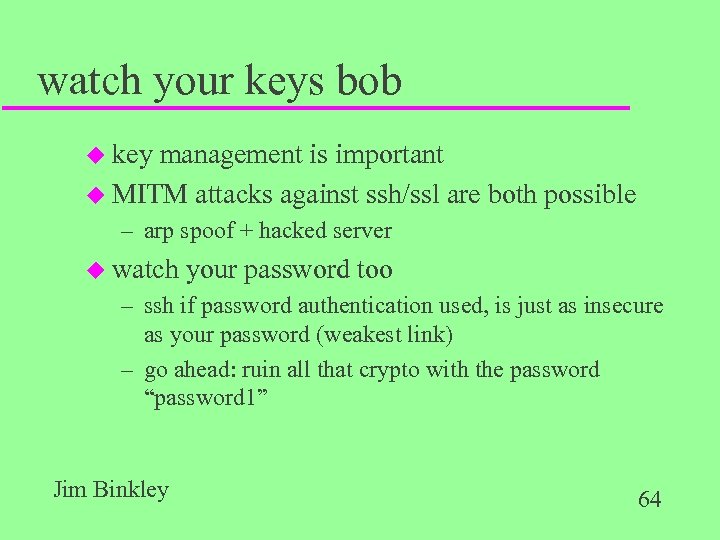
Advanced malware and hackers collect SSH keys and use them to spread attack. Can spread to thousands of servers in minutes, take down an enterprise.